IoT Penetration Testing: Real Findings from 7 Enterprise IoT Devices


Smart building infrastructure is now standard across enterprise Malaysia — IP cameras, video intercoms, facial recognition terminals, and NVRs are deployed at scale. IoT penetration testing Malaysia reveals these devices are rarely as secure as assumed — most organisations trust them by default. They’re “just cameras.” They’re “just speakers.”
That assumption is exactly what attackers rely on.
This article draws from a real IoT penetration testing engagement our team conducted in Malaysia, where we physically disassembled and security-tested seven enterprise IoT devices. We’ll show you what we tested, how we tested it, what we found — including a live firmware extraction — and why Chinese-branded IoT devices deserve a closer look before deployment.
What Is IoT Penetration Testing (IoT VAPT)?
IoT Vulnerability Assessment and Penetration Testing (VAPT) is a hands-on security assessment of connected devices — covering hardware interfaces, embedded firmware, communication protocols, and supporting services.
Unlike a web application pentest (which you can run remotely), IoT security testing requires physical access to the device. Our testers probe actual circuit boards, read firmware from memory chips, intercept serial communications, and test hardware-level weaknesses that network-only scanning would never discover.
The core question we answer: if an attacker had physical access to your IoT device — a disgruntled employee, a third-party contractor, or someone with 15 minutes alone in a server room — what could they do?
The Scope: 7 Enterprise IoT Devices Tested
The following device types, commonly found in smart building and physical security environments, were assessed:
Each device was physically inspected, disassembled where possible, and subjected to hardware-level security testing using both manual techniques and specialist tools.
Our IoT Penetration Testing Methodology
We follow a structured five-phase approach:
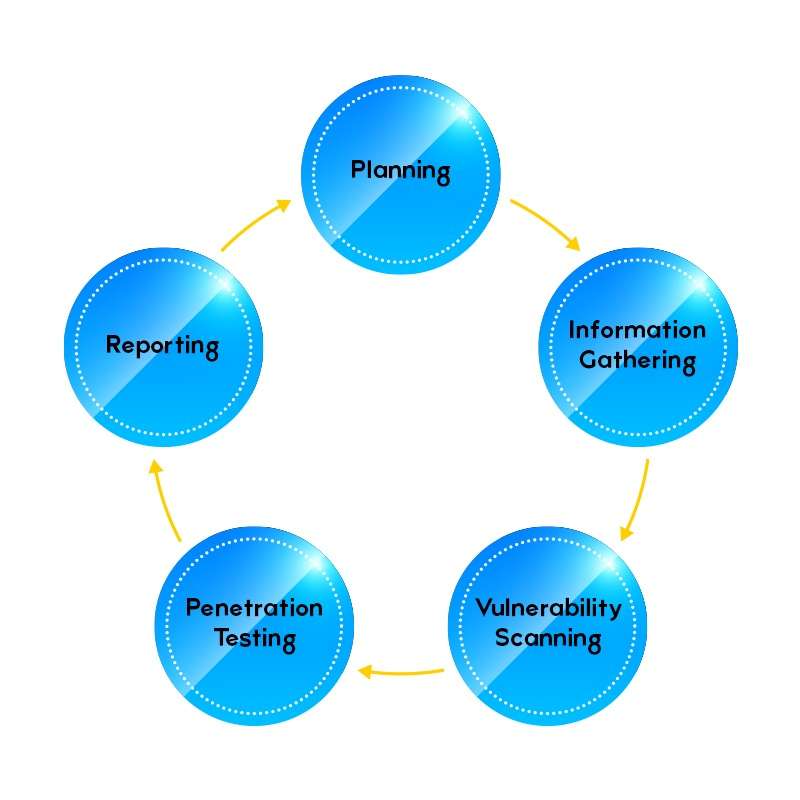
In the Planning phase we define scope, objectives, and the attack surface for each device. Information Gathering covers physical inspection — identifying UART, SPI, I2C, JTAG headers, memory chips, and chip markings. Vulnerability Scanning systematically maps weaknesses. Penetration Testing involves controlled exploitation with proof-of-concept evidence. Reporting documents findings using CVSS scoring with actionable remediation guidance.
Tools We Use for IoT Hardware Security Testing
| Tool | What It Does |
|---|---|
| Multimeter | Detect GND by continuity, measure voltage, identify UART TX/RX pins on PCB |
| CH341A USB Programmer | Read, erase, and write 24-series EEPROM and 25-series SPI flash chips |
| UART Connector | Bridge TTL serial from microcontrollers to a USB COM port — enables console access |
| Flashrom | Open-source tool to dump, erase, or write firmware binaries from flash chips |
| SOIC8 Clip | Clips directly onto the flash chip pins without desoldering — zero-invasive firmware extraction |
Vulnerability Summary: What We Found
Across all seven devices, we identified one medium-severity vulnerability affecting a display controller. The remaining six devices demonstrated strong built-in security controls.
Vulnerability Findings by Severity — 7 Devices Tested
Critical
High
Medium
Low
High
Medium
Low
0 High
1 Medium
0 Low
1 medium-severity finding identified across 7 enterprise IoT devices — no critical or high-risk vulnerabilities.
Key Finding — Insecure Flash Memory Storage
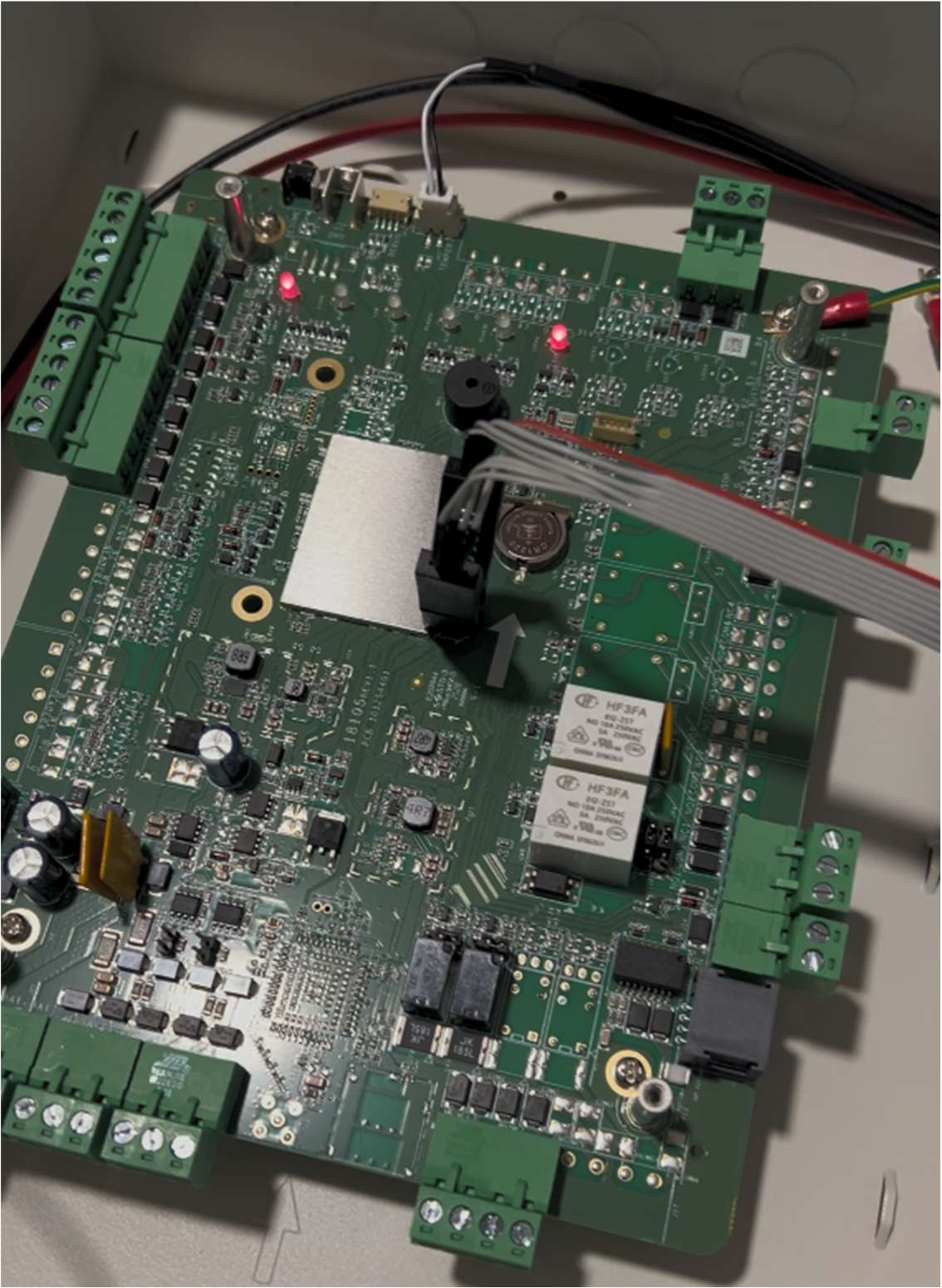
Insecure Flash Memory Storage on IoT Device
Affected component: Display Controller — Physical SPI Interface
Impact: Sensitive data including hardcoded credentials, cryptographic keys, configuration files, and proprietary firmware may be extracted by anyone with brief physical access to the device.
How It Works — The Attack
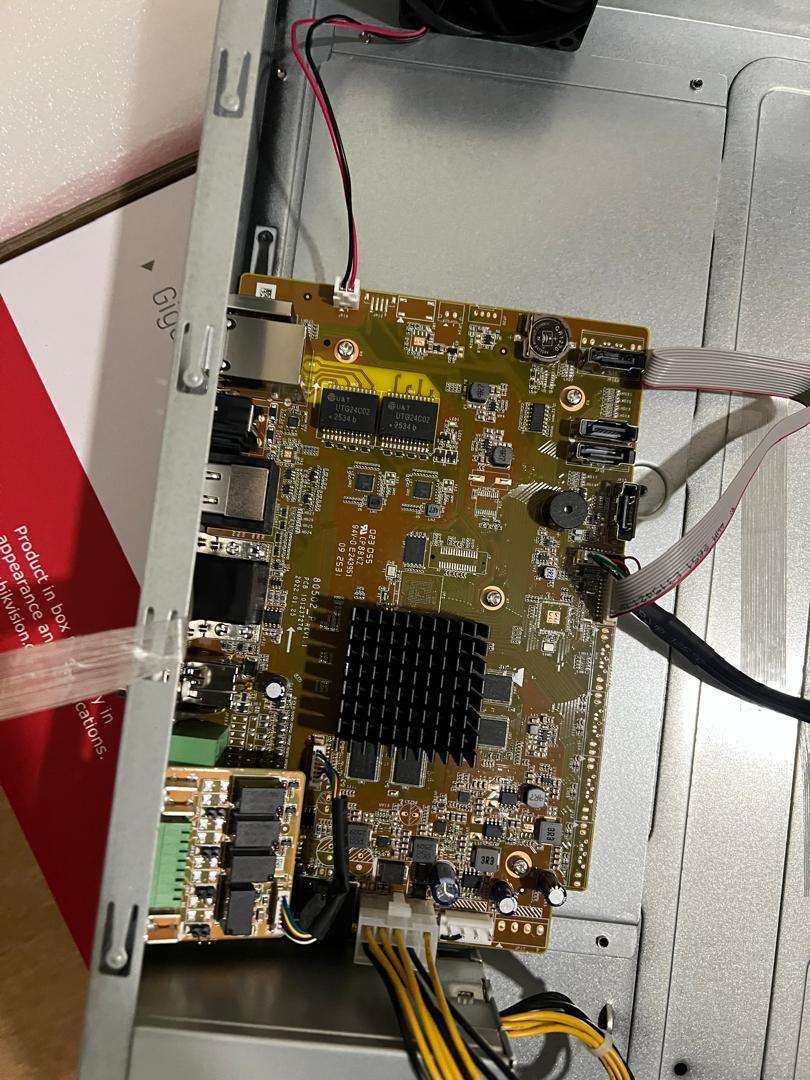
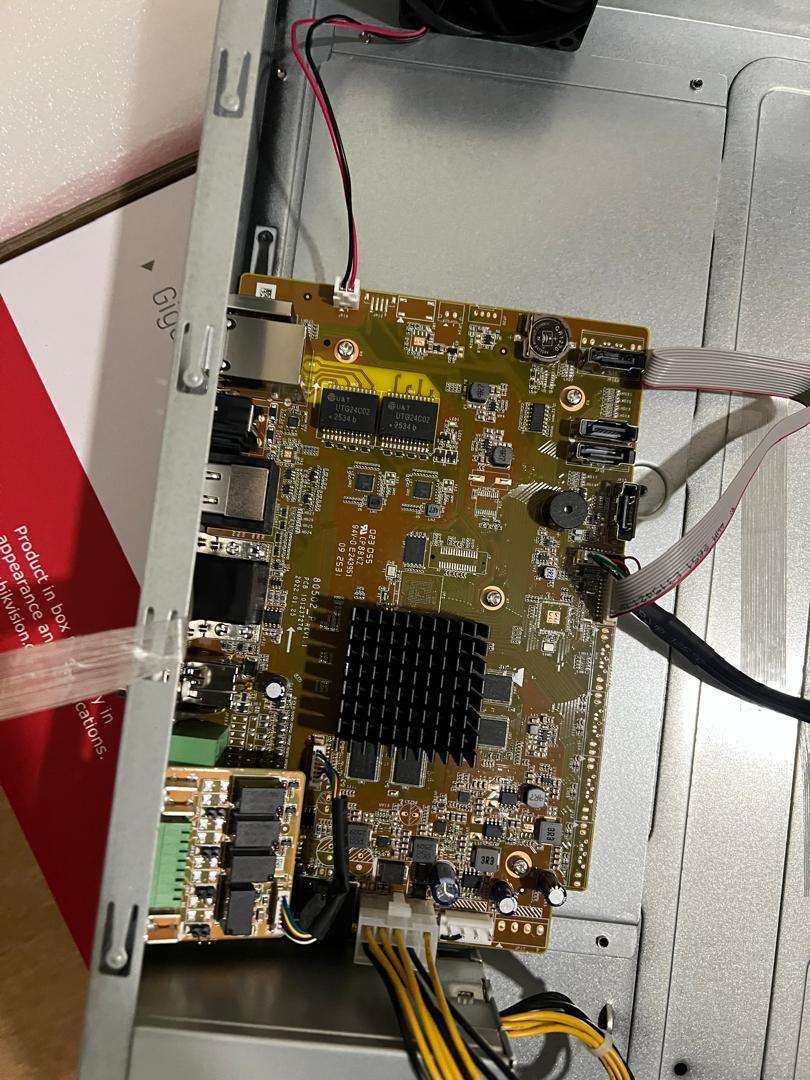
The display controller’s SPI flash memory chip sat exposed on the PCB with no physical protection, no read-lock, and no access authentication. Using a SOIC8 clip (a small clamp that grips directly onto the chip’s pins without any soldering) connected to a CH341A USB programmer, our tester attached the clip to the chip in under 60 seconds:
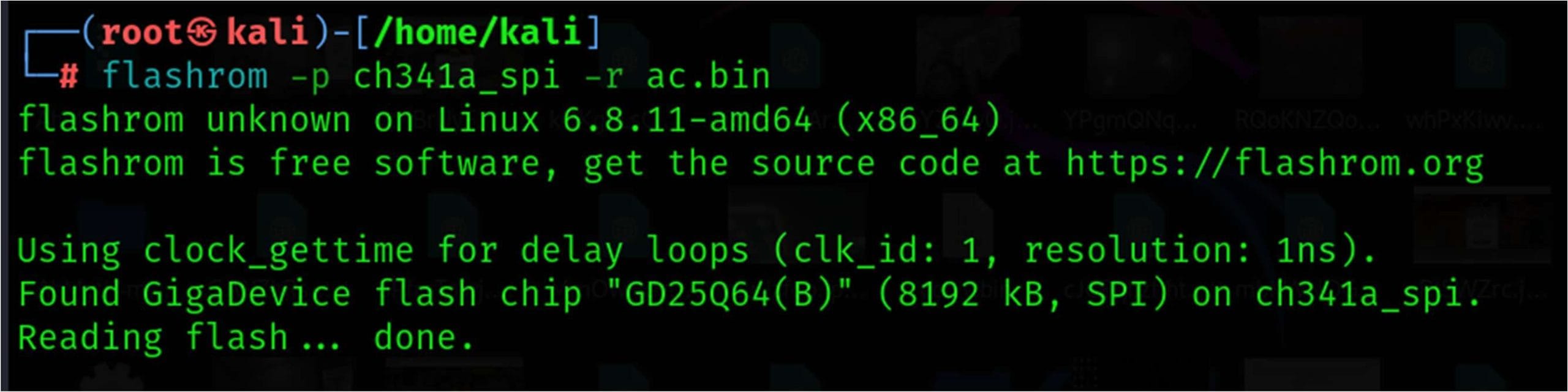
With the clip in place, a single flashrom command was run on Kali Linux:
flashrom -p ch341a_spi -r firmware.bin
The entire 8MB of flash memory was dumped in seconds. The tool confirmed: no authentication or protection blocked the read.
What an Attacker Can Do With the Dump
- Recover credentials in plaintext — usernames, passwords, API keys stored without encryption
- Perform offline reverse engineering — analyse proprietary logic, cryptographic implementations, hardcoded secrets
- Reflash a backdoored firmware — write modified firmware back to the chip to establish persistent, undetected access
- Use extracted config to pivot — network credentials or authentication tokens found in the dump can be used to access other connected systems
Remediation Recommendations
| Control Area | Action Required |
|---|---|
| Physical Security | Tamper-resistant casing, sealed enclosures, tamper-evident labels. Restrict physical access to authorised personnel only. |
| Flash Memory Protection | Enable read protection / flash lock (if chipset supports). Disable debug interfaces (JTAG, UART, SPI) in production firmware. |
| Data Protection | Encrypt all sensitive data in flash using AES-256. Never store plaintext credentials. Use TPM or secure element for keys where available. |
| Firmware Integrity | Implement firmware signing and verification. Enable secure boot. Detect and prevent unauthorised reflashing. |
| Monitoring | Log all firmware update events. Alert on abnormal hardware maintenance activity. Monitor for unauthorised programmer device connections. |
The Chinese-Brand CCTV Question: Should You Be Concerned?
⚠ Why Chinese IoT Brands Are Under Global Scrutiny
Several of the most widely deployed CCTV and IoT brands in Malaysia — including Hikvision and Dahua — are Chinese state-linked companies. Their devices are embedded in offices, hospitals, government buildings, data centres, and critical infrastructure across the country. Internationally, governments have taken increasingly firm positions on these brands.
What Global Regulators Have Said
- United States (FCC, 2022): Banned Hikvision and Dahua from receiving new equipment authorisations. Classified as “unacceptable national security risks.”
- United Kingdom (Cabinet Office, 2022): Ordered removal of Chinese-made surveillance cameras from government “sensitive sites.” Parliament passed a ban on new installations.
- Australia (2022): Ordered removal of Hikvision and Dahua cameras from Defence buildings.
- Lithuania, India, Taiwan: Various restrictions or guidance advisories on Chinese-brand surveillance hardware in sensitive environments.
The Core Security Concerns
- Backdoor risk: Historical CVEs have documented undocumented backdoor accounts (e.g., CVE-2021-36260 — Hikvision remote command execution via web server, CVSS 9.8 Critical). These are not theoretical — they were exploited in the wild.
- Forced cloud connectivity: Many devices are preconfigured to call home to Chinese cloud infrastructure, creating persistent data exfiltration channels even when used on isolated networks.
- Firmware supply chain risk: Devices may ship with firmware developed under Chinese government oversight, with no independent third-party security audit.
- Weak default credentials: A significant proportion of deployed Hikvision/Dahua devices in Malaysia still use factory default passwords — trivially exploitable remotely.
- Limited transparency: Independent security researchers face barriers to responsible disclosure, and firmware source code is proprietary.
What Our Testing Found
During this engagement, the enterprise-grade CCTV cameras tested demonstrated strong hardware security controls at the device level — including a secure boot chain, encrypted firmware updates, anti-rollback protection, and no exposed JTAG/UART debug interfaces. Physical testing confirmed the camera casing was vandal-resistant (IK10 rated), successfully resisting all physical access attempts:
This is an important distinction: hardware-level firmware security can be strong while network-level and cloud-connectivity risks remain. A device can pass physical hardening tests and still phone home to external servers, use default credentials over the network, or be vulnerable to remote firmware exploits (like the CVE-2021-36260 RCE mentioned above).
Our Recommendation for Malaysian Organisations
- Segment IoT devices onto a separate VLAN with strict firewall rules. Block outbound connections to Chinese cloud endpoints unless explicitly required.
- Change all default credentials immediately upon deployment — this alone eliminates the majority of opportunistic attacks.
- Disable P2P/cloud features if remote access is not required. These features create unnecessary attack surface and data exposure.
- Conduct IoT VAPT before deployment — both physical hardware testing and network-level assessment. Do not assume vendor security claims are accurate.
- For sensitive environments (government, financial services, healthcare, critical infrastructure): consider procurement policies that explicitly exclude devices from vendors with national security risk designations in allied countries.
- Reference NACSA guidelines for IoT devices deployed in critical national information infrastructure (CNII) environments.
Devices That Passed: What Good IoT Security Looks Like
Six of the seven devices tested showed no exploitable vulnerabilities. The security controls validated during physical testing included:
✅ Security Controls Confirmed in the Field
- Secure boot chain — prevents unauthorised firmware from executing at startup
- Encrypted firmware update packages — update files are cryptographically signed and verified
- Anti-rollback (anti-degradation) protection — blocks downgrade to older vulnerable firmware versions
- No exposed JTAG/UART debug interfaces — debug access eliminated in production hardware
- Restricted access to firmware and memory components — physical hardening resists chip-level attacks
- Hardened PCB architecture — board layout designed to resist tampering


How IoT VAPT Maps to PDPA Compliance in Malaysia
Under Malaysia’s Personal Data Protection Act (PDPA), organisations processing personal data — including CCTV footage, facial recognition biometrics, and access logs — must take reasonable security steps to protect that data from unauthorised access or disclosure.
An IoT device with unprotected flash memory (like the finding in this report) is a direct PDPA risk: if an attacker extracts credentials from the device and accesses the surveillance system, the CCTV footage of employees, visitors, and customers becomes a PDPA data breach.
| Framework | Reference | How This Applies |
|---|---|---|
| OWASP IoT Top 10 | I4 — Insecure Update Mechanism | Firmware extractable without authentication verification |
| OWASP IoT Top 10 | I8 — Lack of Physical Hardening | Flash chip accessible, no tamper protection |
| Malaysia PDPA | Security Principle (s.9) | Reasonable steps required to protect PII from unauthorised access |
| NACSA Cybersecurity Act 2024 | Physical Security Controls | IoT in critical environments must have physical access controls |
| BNM RMiT | Technology Risk Management | All connected devices in financial institutions require security assessment before deployment |
Frequently Asked Questions About IoT VAPT
Is Your IoT Infrastructure Really Secure?
Our team provides hands-on IoT penetration testing across Malaysia — from smart building devices to industrial controllers. We test what others can’t: the hardware itself. CREST-accredited, NACSA-licensed, Malaysia-based.
Get a Free IoT Security Consultation →
No commitment required · Response within 1 business day


